Security architecture
Bloomreach runs on Google Cloud Platform (GCP) and uses multiple layers of security to protect your customer data. This guide explains how data is encrypted, how the platform is architected for resilience, and how each instance type is isolated and secured.
Security overview
The visualization below illustrates the 3 instance types available. The upper portion shows how data in transit is secured and encrypted before entering Bloomreach. The lower portion shows a high-level overview of the platform architecture and the security features available for each instance.
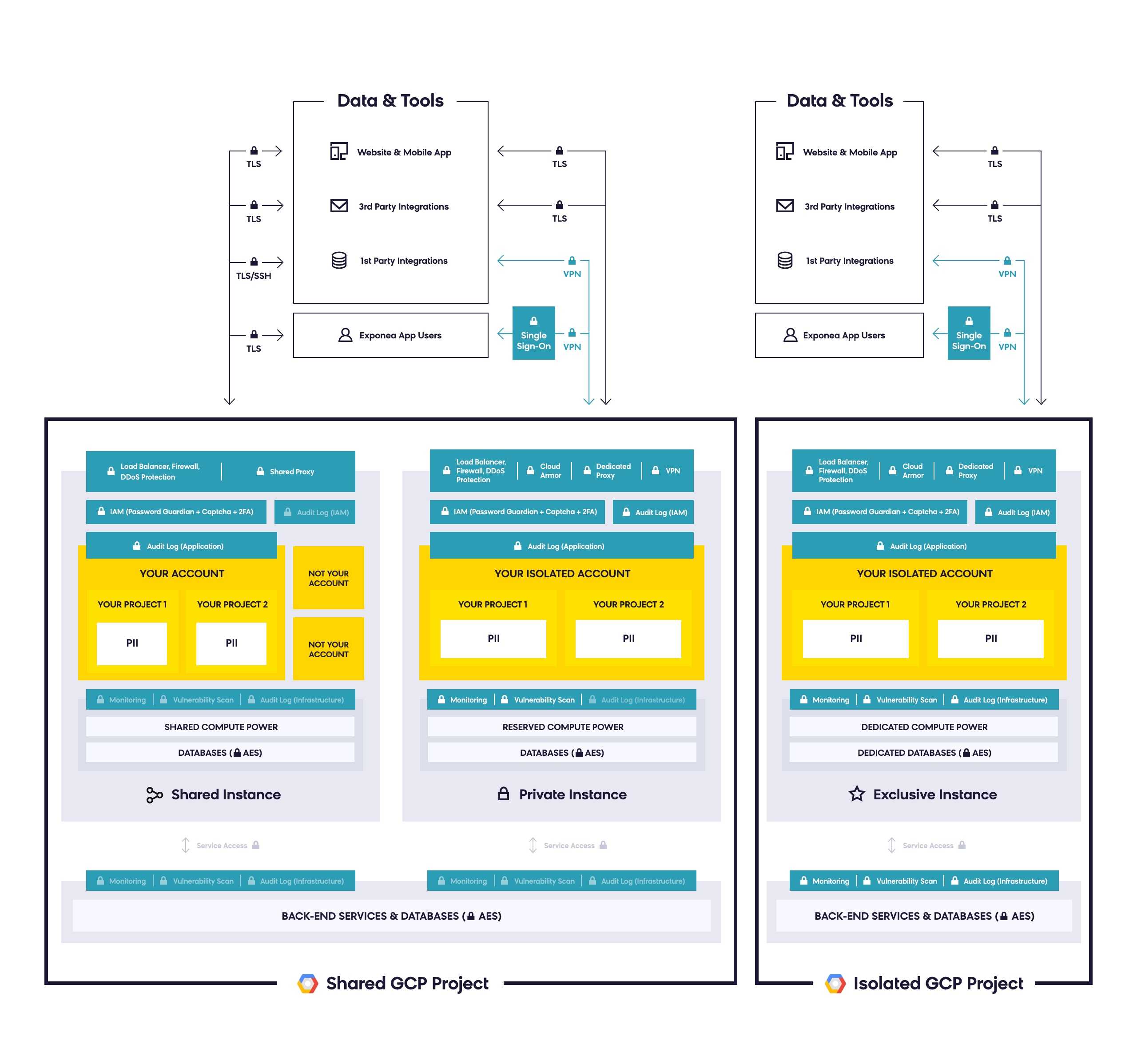
High-level security architecture diagram showing encryption in transit and instance-level security features.
Encryption
All stored data is encrypted by default — both at rest and in transit.
Encryption at rest
Encryption at rest protects your data in the event of a system compromise or data exfiltration. Bloomreach uses the Advanced Encryption Standard (AES) to encrypt stored data. Encryption keys are managed by Google.
Encryption in transit
Encryption in transit protects your data if communications are intercepted while data moves between your site and the cloud provider. This is achieved through Transport Layer Security (TLS), which:
- Encrypts data before transmission.
- Authenticates the endpoints.
- Decrypts and verifies the data on arrival.
TLS acts as a tunnel to separate data from the outside environment, with encryption keys exchanged between endpoints. GCP also encrypts and authenticates all data in transit at one or more network layers when data moves outside physical boundaries not controlled by or on behalf of Google. Data in transit inside a physical boundary controlled by or on behalf of Google is authenticated but not necessarily encrypted. Encryption keys are managed by Google. For details, see Encryption in transit in Google Cloud Platform.
Third-party data transfer
When data is transferred via a third party—for example, Mailgun or Sinch—it's protected and transferred using HTTPS.
Architecture
GCP runs in a multi-tenant, geographically distributed environment to support service availability. Data is distributed across a shared infrastructure designed to store extremely large amounts of data across many servers.
Bloomreach has also built a highly available and resilient architecture that replicates data in real time across multiple zones and data centers. This enables high availability through dynamic load balancing across those sites.
Instances
Bloomreach offers three instance types:
- Multi-tenant
- Single-tenant
- Exclusive
Each type has a different configuration of data layers and security features. In all instances, data is separated and access management is enabled.
Multi-tenant instance
The multi-tenant instance is designed for SMEs that aren't subject to strict regulatory requirements.
In this instance, users can't access data from other clients. Data is separated at the frontend level, and resources are shared at the backend level. The instance is encrypted at the GCP infrastructure level and undergoes periodic security scans and penetration tests.
To access the account, users must set a strong password and can enable two-factor authentication (2FA). Accounts are also protected by a captcha to prevent bot attacks. Project admins can specify in Access management which users can view customer PII. This distinction applies at both the frontend and backend levels.
Included features
- Captcha
- Data encryption (SSL/TLS and AES)
- DDoS protection
- Firewall
- Identity Access Management (IAM)
- Password guardian
- Single sign-on (SSO)
- SSH tunnel
- Static IPs
Available as add-ons
- Audit log report access: IAM and application
- Custom SSL
- IP restriction
- SSO (SAML2)
Think of the multi-tenant instance as a building with multiple offices, each with a security door. All clients share a single GCP environment but have separate accounts and passwords, with data segregation between instances.
Single-tenant instance
The single-tenant instance is designed for multinational brands that require a higher level of data security and face tougher data scrutiny.
In this instance, data layers are logically separated at the backend. Computing resources reserved for the client are separated from other resources by namespace. The instance is encrypted at the GCP infrastructure level and undergoes periodic security scans and penetration tests.
To access the account, users must set a strong password and can enable 2FA. Accounts are also protected by a captcha to prevent bot attacks. Project admins can specify in Access management which users can view customer PII. This distinction applies at both the frontend and backend level.
Included features
- Captcha
- Data encryption (SSL/TLS and AES)
- DDoS protection
- Firewall
- Identity Access Management (IAM)
- Password guardian
- SSH tunnel
- Static IPs
Available as add-ons
- Audit log report access: IAM and application
- Custom SSL
- IP restriction (Cloud Armor)
- SSO (SAML2)
- Virtual Private Network (VPN)
Think of the single-tenant instance as separate buildings that share only an electricity supply. Each instance runs within a separate capacity, powered by GCP.
Exclusive instance
The exclusive instance is designed for large companies with strict regulatory obligations that handle sensitive categories of data.
This instance provides complete segregation of logical layers and full network separation through a dedicated GCP project and dedicated backend computing resources. Access rights and permissions are also fully separated.
The instance is encrypted at the GCP infrastructure level and undergoes periodic security scans and penetration tests. It also supports SSO to meet industry security standards. Accounts are protected by a captcha to prevent bot attacks. Project admins can specify in Access management which users can view customer PII. This distinction applies at both the frontend and backend level.
This platform includes complete segregation of logical layers and network separation through utilizing a different GCP project and backend computing resources dedicated to you. Within the exclusive instance, there is also the separation of access rights and permissions.
In addition to the standard security features, the exclusive instance gives you:
- Log administration: Stream logs to your SIEM.
- Emergency brake: Cut off Bloomreach from production at any time.
- Backend configuration: Switch on new Google services, network settings, or access rights to the backend architecture.
Included features
- Captcha
- Data encryption (SSL/TLS and AES)
- DDoS protection
- Firewall
- Identity Access Management (IAM)
- Password guardian
- SSH tunnel
- Static IPs
Available as add-ons
- Audit log report access: infrastructure, IAM, and application
- Custom SSL
- IP restriction (Cloud Armor)
- SSO (SAML2)
- Virtual Private Network (VPN)
Instance comparison
| Separation layers | Multi-tenant | Single-tenant | Exclusive |
|---|---|---|---|
| Data layer | Your data is visible only in your accounts and projects. | Your data is visible only in your accounts and projects. | Your data is visible only in your accounts and projects. |
| Users layer | Users authorized only for your accounts and projects. | Users authorized only for your accounts and projects. | Users authorized only for your accounts and projects. |
| Frontend layer | Application settings, definitions, and campaigns visible only within your projects. | Application settings, definitions, and campaigns visible only within your projects. | Application settings, definitions, and campaigns visible only within your projects. |
| Backend layer | Shared network, shared databases, shared Kubernetes cluster. | Logically separated network and all backend services, shared and dedicated databases, shared Kubernetes cluster. | Network separated from scratch, dedicated databases, dedicated Kubernetes cluster. |
| Infrastructure administrator access | Shared administrator accesses. | Shared administrator accesses. | Administrator accesses established from scratch. |
ImportantAlthough the infrastructure is built on GCP, File management in the Asset Manager is an exception. The location of files and data stored in the Asset Manager isn't guaranteed. Storing sensitive content in the Asset Manager isn't recommended.
Updated 2 months ago
