Two-step verification
Two-step verification is a more secure way to protect your accounts. It combines a password (something you know) with a second factor (something you own), making it harder for attackers to gain access.
The 2 most common verification methods are:
- Text message: A PIN code sent to your mobile phone.
- Authenticator app: A time-based code generated on your device
Set up two-step verification
To enable two-step verification, under Settings > User settings go to Security.
Once enabled, you're asked to verify your identity with the chosen method every time you log in. You're also asked for a new code after 30 days or whenever your IP address changes.
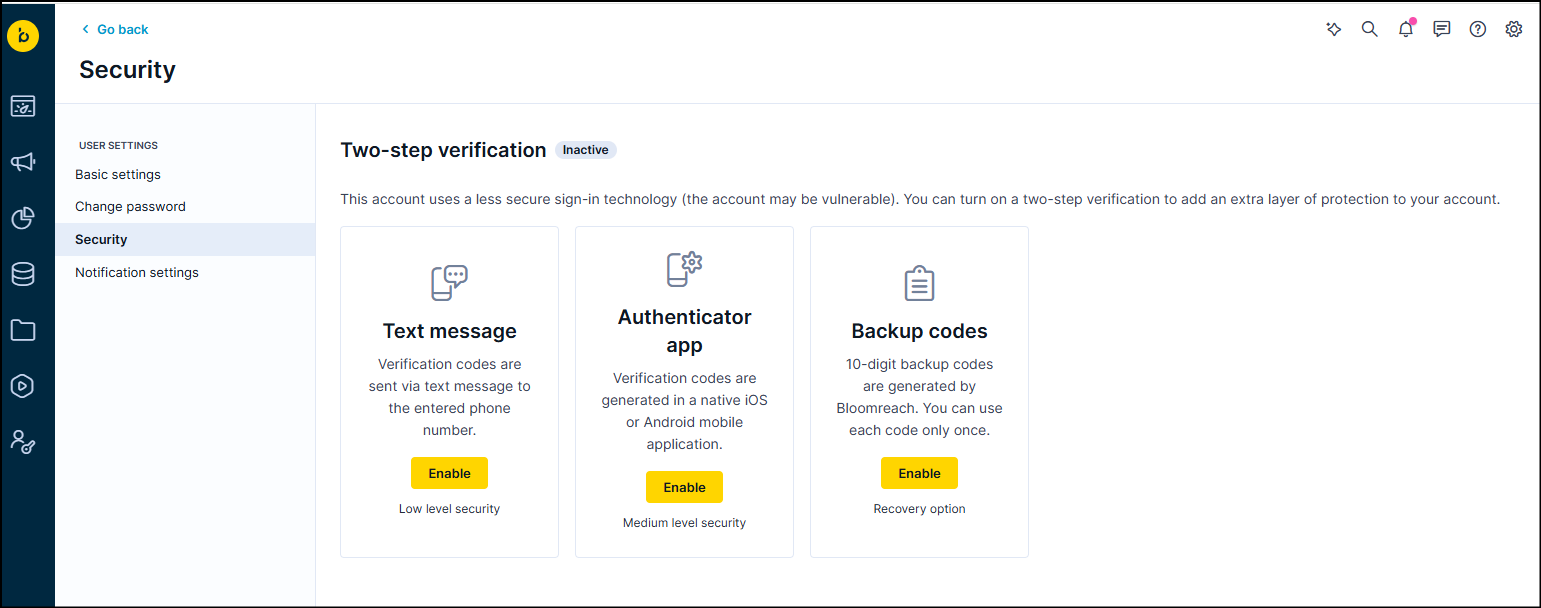
Text message
- Enable the Text message option.
- Enter your phone number and click Get code.
- Enter the 6-digit code you got, then click Confirm.
Authenticator app
- Enable the Authenticator app option.
- Install an authenticator app on your mobile device. We recommend Google Authenticator (iOS or Android), but any authenticator app works.
- Open the app and scan the QR code to get a 6-digit code.
- Enter the code, then click Confirm.
Backup codes
Backup codes let you log in if you don't have access to your mobile device. When you enable this option, you get 10 single-use codes. Store them somewhere secure.
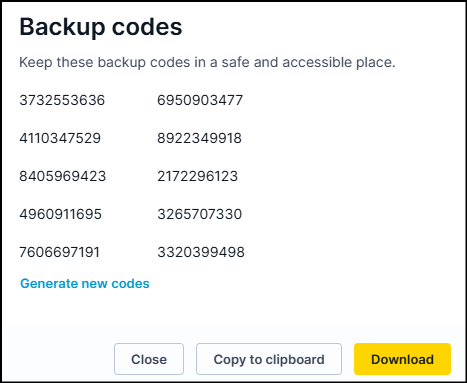
Example backup codes
NoteBackup codes aren't part of two-step verification itself. They're a recovery option only. Use them if you lose access to your device.
Enforce two-step verification
You can make two-step verification mandatory for all users on a project or account. Go to Project or Account settings > Security > Two-step verification.
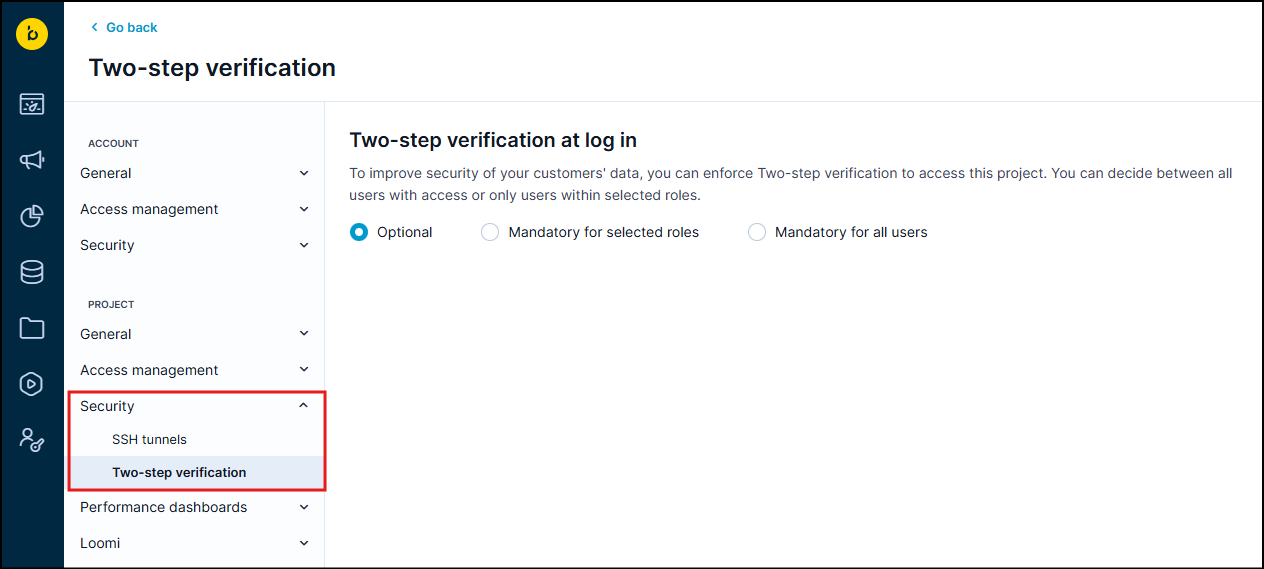
Settings can only be changed by a Project admin. There are 2 options:
- Optional: Users can choose whether to use two-step verification (default).
- Mandatory for all users: Every user with access to the account or project must use two-step verification.
We recommend that users download backup codes when setting up two-step verification. This option is available on the same settings page.
Force existing users to enroll
Setting two-step verification to mandatory doesn't automatically force existing users to re-authenticate or complete enrollment. Users who were already logged in when you made the change may remain active without enrolling.
To force enrollment, a Cloud Org Admin can terminate individual user sessions. Once a session is terminated, the user has to log in again and set up two-step verification before they can continue. Note that:
- You can only terminate sessions for users in the same identity domain.
- There's no bulk action. Sessions must be terminated one user at a time.
If terminating sessions manually isn't practical, you can wait for sessions to expire naturally instead. The default session length is 24 hours, but sessions extend as long as the user stays active. If a user opens the browser tab every day, their session can last over a month. To gauge timing, check each user's last login time before deciding whether to wait or terminate manually.
Reset two-step verification
If you change your phone number or lose your device, you need to reset two-factor authentication (2FA) to regain access. To request a reset:
- Submit a 2FA reset request to Support, either yourself or through a colleague.
- Support verifies the request and sends a confirmation email to the address associated with the account.
- Reply to the email to confirm the request is valid.
- Once support receives your confirmation, they reset 2FA for the account.
- After the reset, set up a new 2FA method and log in.
Troubleshooting
Google Authenticator codes not working
If your codes have stopped working or are showing an error, the most likely cause is a time sync issue.
- Open the Google Authenticator app.
- Go to the Menu > Settings > Time Correction for Codes.
- Click Sync Now.
This will automatically correct the time.
Sync time on your device
Go to your device's Settings > Date & Time and turn on automatic time and timezone.
Lost or damaged device
If you've lost your device or it's not working, use your backup codes to log in. This is why it's important to generate and store backup codes securely when you first set up two-step verification.
Updated 2 months ago
